We are waking up in the UK to news that Talk Talk, the telecoms provider, has sustained a “persistent attack” on Wednesday 21st October 2015.

The details the CEO has disclosed about the attack are as follows (Source LINK):
- Attack happened in the morning.
- Web servers were taken down by lunchtime.
- Met Police and security advisers were called to investigate
- Too early to say what was attacked and what was stolen.
- Potentially all customers are affected.
- CEO was potentially on the list.
- Phasing the servers they are bringing up when they know they are safe.
- Met Police has an open investigation
- Compensation – all customers will receive a year’s free credit monitoring
- It is a potential threat at the moment – the scale is unknown
(as at 08:44 23/2015).
As this story unfolds, we will learn more about the size of the breach in terms of numbers of records stolen as well as the depth of that data. Note to self : they were compromised last year via 3rd partied : (LINK) and have had 3 attacks since February.
Their current thoughts are that the following data may have been compromised :
- Names
- Addresses
- Dates of birth
- Email addresses
- Telephone numbers
- Talk Talk account information
- Credit card details and/or bank details
This is obviously a concern as this information could be used in identity theft.
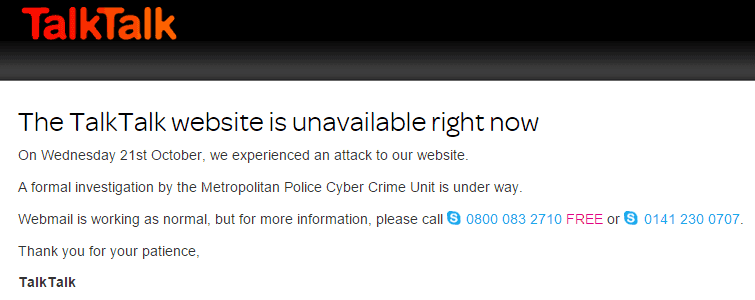
The Talk Talk website for My Account was closed so users could not change their log-in credentials :
When calling the customer service number, you are on hold for about 10 minutes before being connected to the Indian call centre handling the calls.
The advice from them was that yes, the website will remain offline for now and that all customers should monitor their bank accounts and call Action Fraud should they see anything unusual. All customers will be notified once they can go back in to the websites.
I found this advice interesting for a number of reasons. As a customer of Talk Talk, it is fairly clear that they have fairly robust password changing systems and I am fairly confident that passwords would be encrypted (to what level is unknown) and under the usual advice the security world would place here, it is important that customers should choose .
What is a puzzle is :
- they have not given people access to change those credentials meaning that if the criminal does have this data, it is clear they cannot do much with it (it may be fairly well encrypted or not a complete dataset)
- that customers should focus on the possibility of a financial attack.
It is this second point that I am most intrigued by. Does this mean that once inside the databases of Talk Talk, they were able to pivot from one table to another to pick up the financial records ? With the fear being focussed about this side of the data, the risk of the criminal using it must be higher therefore the data must be more accessible. Speculation would say that the encryption was lower perhaps ? However, their own site says they do not store credit card details (LINK) but the advice given above suggests that credit card data may have been stolen.
As Talk Talk are a regulated body and receive such a high amount of payments, they come under the regulation of PCI DSS compliance (confirmed here). This is an advantage in that it would also infer that regular security testing is in place, monitoring and all the other parts of the compliance. If this is the case, maybe this is why they were able to jump on it within a couple of hours ?
On the encryption side of the discussion comes this from their website under FAQs :
Was the data encrypted? If not, why not?
Not all of the data was encrypted. We constantly review and update our systems to make sure they are as secure as possible. We’re working with the police and cyber security experts to understand what happened and protect as best we can against similar attacks in future.
This is a very interesting admission and shows they may not have been compliant.
I believe their will be some pen testing companies and auditors dusting down their reports to check that they did everything right.
Who did it ?
Well, the current theory is Russian Jihadists. This was posted yesterday evening 22nd October 2015 :
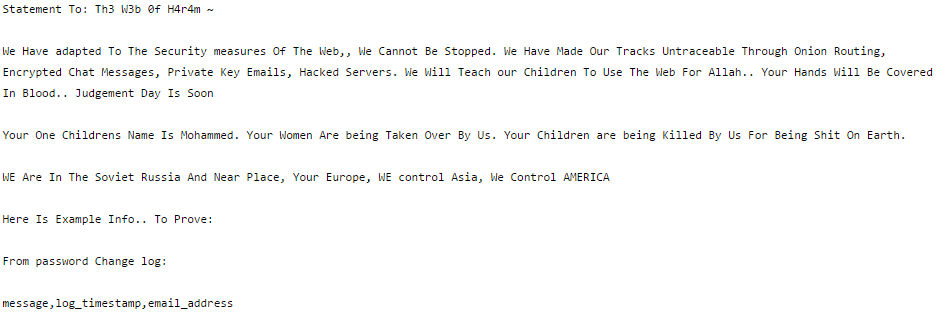
However, this only appeared after news went public from Talk Talk about the breach.
There also appear to be in circulation a list of 64 databases posted yesterday 22nd October 2015 :
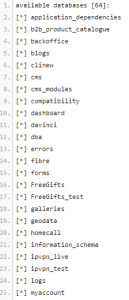
Again, there is no evidence or proof that this list is complete or accurate. However, there are tables in there called myaccount and homecall which would seem consistent with an expected dataset.
The infrastructure
Looking through the job websites, I noted that there is a lot of recruitment happening within Talk Talk, but this also gives us some insight into the technologies they use and where the potential gaps in their skill set lie at the moment:
IT Systems : (including past experience in development, for example, .NET, C#, C++, Java, SQL, Oracle)
Virtualisation : no technologies listed
Hardware/Software : HP kit, Windows, Linux, Solaris, AIX
Networking : Cisco, Juniper,
Databases : (Proven DBA experience of MySQL and/or MS SQL) with Oracle skills
Methodologies : Familiarity of ITIL working practices
ISO Compliance : ISO knowledge
Audit : Develop scope and planning for internal audits and integrated audits.
Security : policy, SPC, ISMS (which shows ISO27001), pen testing
An interesting list indeed and maybe shows their growth ? Maybe the skill set shortages they have are due to a victim of their own success ?
It is fairly evident that this is a breaking story with so much unknown about the incident and with the Met Police involved, the details should also be slow to come out in case it prejudices the case at all.
If you do become a victim of this crime, please contact :
Action Fraud UK
http://www.actionfraud.police.uk/
Telephone : 0300 123 2040
Good Luck and Stay Safe!
Stuart Coulson @SPCoulson
Current open job for Information Security Officer job advertised here LINK if anyone is interested.
UPDATES :
10:40
Some un-confirmed rumours surfacing of a DDoS on Talk Talk yesterday. However, likely explanation for this rumour here by Robert Schifreen.
@iblametom@BBCTech@ruskin147 They’re reading between the lines of the TT statement on it being a “sustained” attack.
10:49
After an initial share price drop for Talk Talk, shares are now starting to rally slightly.
11:09
MyAccount and sales websites remain offline, 24 hours after initial attack.
11:14
Vendor has scanned the site and claims it is not Compliant : LINK – also picked up on my LinkedIn profile.
11:26
Trolling or is the data public ?
LINK to tweet
11:31
This twitter account here is also putting some attribution to the user above.
11:33
Odd info in a new leaked database table list – why have an advertisement in a database ? This would cause massive database tables.
EmployeeID,EmployeeTypeID,PCUserName,EmployeeDate,EmployeeType,EmployeeName
[12:58:31 AM] VAMP – The SMITE Smasher: ID,referenceID,name,abuse,status,comment,username,IPaddress,timestamp
93,ANONYMIZED,alex,2008027,1,”\r\nAdvertisement starts\r\n\r\n——————————————————————————–\r\n\r\n\r\n\r\n——————————————————————————–\r\n\r\nAdvertisement endsRelated Links\r\nCoen brothers positioned for Oscar \r\nScreen Actors laud Coen brothers \r\nScreen Actors laud “”No Country For Old Men”” \r\n””No Country for Old Men”” tops Screen Actors awards \r\n””Ratatouille”” and “”Bee Movie”” make Oscar shortlist \r\n\r\nNews Headlines\r\nCoen brothers positioned for Oscar \r\nLed Zeppelin concert off until at least September \r\nGang of Four working on new songs \r\nBasshunter tops singles chart for third week \r\nPeers name Coens best directors \r\nDel Toro doubles up to direct big-screen “”Hobbit”” \r\n””Asterix”” film embarks on colossal Euro launch \r\nIndie labels plan global celebration to raise funds \r\nMarlon Brando’s son dies at 49 in L.A. \r\nLegal file-sharing service touts free music with ads \r\n””No Country For Old Men,”” directed by Ethan and Joel Coen, took the award for best ensemble cast and Spanish actor Javier Bardem won the best supporting actor award for playing a cold-blooded killer in the movie.”,ANONYMIZED,ANONYMIZED,2008-01-28 11:52:49
11:44
Also noted from this data leak is that the timestamp is 2008 – maybe not live data ?
12:12
Paul Lewis is posting that this may include data from previous customers of Talk Talk too.
12:15
Personally, we should be ensuring all our passwords are unique and today is as good a day as any to change any passwords we have to ensure they are .
12:40
“There have been no arrests and enquiries are ongoing.” says Met Police
13:12
BBC is reporting the hack was by DDoS. This may have been a distraction from the real attack as a DDoS does not exfiltrate data.
13:15
BBC also reporting that a ransom email was received by the Head of TalkTalk.
13:33
FireEye reporting having seen Talk Talk data for download on criminal websites.
13:48
Update from latest press briefing :
- Criminals not only threatening data leak but also persistent DDoS
- They could have done more – but every company is in this same state
- They cannot guarantee all data was encrypted.
13:48
eMails have started to be received by customers telling them about the breach. No new information contained in there that hasn’t already been in the press.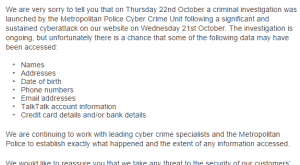
14:12
Talk Talk boss is now starting to look tired after very little sleep over this, and I guess some engineers will look the same. Good luck to the team.
Press interview facts :
- The 3 attacks they have had are un-related.
- Letters are sent also
- Talk Talk are highlighting the possibility of phishing scams.
- First indication was Wednesday lunchtime when the website was running slowly.
- Still don’t know how many records are affected.
My takeaways are that the incident response is working well, all customers are now alerted, site and data is locked down to prevent further data leakage, they have investigators doing what they should be doing which is containing the incident and investigating. It was not Dido who has mentioned about the ransom, that was a spokeswoman. Dido’s comment on the matter was:
TalkTalk’s chief executive Dido Harding told the BBC: “Yes, we have been contacted by – I don’t know whether it’s an individual or a group purporting to be the hacker. I personally received a contact from someone purporting – as I say, I don’t know whether they are or are not – to be the hacker, looking for money.
14:19
Tweets on the topic are in the order of 50 per minute. New announcements are now hard to identify, mainstream media is now creating significant content on this topic.
17:15
Is this the first victim of the Talk Talk breach ? Direct Debit purchase at 3am was declined by Santander. She is also unable to get through to the helplines. Assumption that it was Talk Talk but no way to verify where the attacker got their data from. Further highlighting the problem of attribution in online crime.
17:27
Final edit for this story today
Summary
- On the morning of the 21st October Talk Talk noticed that they were having performance issues on their site. This is good news, it means that they were pro-actively monitoring the performance of their site and looking for issues.
- By 11am, the issues were so bad that they suspect a criminal was affecting the performance of their site and they shut the website down and contacted authorities. Well done for contacting the correct authorities and it shows a mature security model with a documented incident response plan, however, by taking the server offline, some damage may have been done to the audit trail.
- Early afternoon, it was clear that a breach had happened but the details were sketchy.
- At around midnight an official press release was sent out to say a breach had happened.
- At approximately 2am, 2 posts were made, one claiming a Russian Jihadist group had done the attack and one claiming the 64 database table names that had been taken
- During the morning of the 23rd, the CEO appeared on as many media outlets as possible to give a consistent message that an investigation was underway and what the worst possible case scenario looked like.
- Just after lunch a threat was made to Talk Talk to say that a ransom was in play. It is unknown if this came from a real adversary or from a tag-on who was trying to profit from this.
We have to put this into a wider context – millions of records are breached every month, some companies go public about it, some do not know the breaches have even happened. Talk Talk is just today’s story. There is nothing new with the scale of this breach when compared to the volume of attacks like Sony or the sensitivity such as the medical data left open. This is a symptom of doing business on the internet and putting data into online systems. This breach is not new, and will not be the last breach. I wish a whole load of good luck to the systems engineers and security staff who are working round the clock on this with very little sleep. I also wish the CEO well – her company is on the rocks and she has nothing but bad news to report until an attacker is found.
Before we throw the CEO on the sword, we also need to identify where it all went wrong – is this due to a CEO not wanting to invest in security? Is it a 0-day, a risk that could not ever be protected from? As this is a live investigation, we are unlikely to know the full information about what has gone on for some time. At some point the criminal will leak the data. The longer they hold on to it, the less value it has as the financial institutes will now be ready and waiting for the adversaries (or so we hope).
The consumer is right to angry and upset. Talk Talk could have done things better and yes, they didn’t get everything right. But as we enter the Christmas shopping season, how many of the websites we put our details into are even less careful with our data as Talk Talk? How will you know which online shop you can trust? Will you still log in with the same username and password for every website? Will your password still be easy to guess? Security starts at the consumers keyboard and ends at the receipt of the goods and services. Each person in that chain adds another layer of security, complexity and therefore also potential weakness.
Good luck to you in your online world, and to all the technicians, engineers and support staff who keep our internet and online worlds as safe as possible.




Leave a Reply