Seven types of cyber criminals: 2024 version
Blog by Stuart Coulson regarding the Seven Types of Cyber Criminal. This is the 2024 and has a new entrant of AI-Enabled Criminals.
Categories:
Tags:
Criminal Hackers
Are all Hackers Criminal Hackers? Are there good and bad Hackers and what is the difference between a Hacker and Criminal?
Categories:
Tags:
CV Tips for people looking for their next role
CV Tips for Technical & Non-technical People to help you land your next role. These tips are from someone who has hired people as well as using them themselves.
Categories:
Tags:
Press Announcement : New Cyber Product Grading System Announced
We are proposing, rather sarcastically, that we use a grading system that has an origin story rooted in the term “Military Grade” and use that to create a benchmark for products and services that companies can use to give their customers faith in their services.
Categories:
Tags:
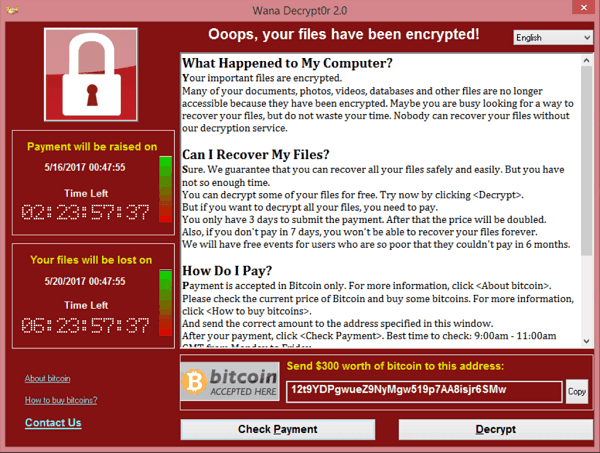
Bitcoin Wallet Blacklist
What if there was a central list of Bitcoin addresses that have been used in malicious activity, that someone can reference to – a Bitcoin Blacklist if you will?”
Categories:
Vacation time for some … playtime for criminals
It’s come to that point in the year, the great annual exodus … holidays … I too am about to go on vacation, but then comes the big debates: What do I put in my out-of-office? How do I address my void on social media? How do I explain why I’m not replying to comments
Categories:
Tags:
2017 – Conference Survival Guide
2017 is flying by, helped by the numerous attacks we are seeing. I usually create one each year and this is now updated as below with stuff I learned from last year. At some point, you will be attending a security conference (hopefully) and from the numerous conferences I have been to, I have put
Categories:
Collection of resources on the NHS Cyber Attack
I thought I would create a page for myself just to keep some idea of the timelines and order of things and to make sense of what I’m reading. How it started : The US intelligence Agency had a 0-day called EternalBlue. EternalBlue looks like this : https://www.youtube.com/watch?v=6rrY0S8x3HQ Approx 14th April 2017 “The ShadowBrokers” leaked this code amongst
Categories:
Tags:
Attribution Bingo
Identifying an individual on the internet is hard. Really hard. There has to be some uniqueness that you can identify to pinpoint down on an individual. That could be style of writing, phrases, icons, avatars, nicknames, names etc. Currently the President of the US is also experiencing this issue. He suspects to have been monitored and
Categories:
Tags:
World Book Day 2017
In honour of World Book Day, I thought I would share with you some ideas for books that I’d recommend. I am an avid reader and so suggestions welcome ! The ones in bold are absolute favourites of mine and I have gone back to them several times. Security Books @Large – Freedman and Mann
Categories:
Tags:
Define, Fun, Hack, infosec, Inspiration, kids, life skills, Personal, security, tips, World Book DayManufacturing Security Standards
This came up in a Brightalk the other day with and Kaspersky and it has really been bothering me. Cyber Essentials At the moment in the UK, SMEs are being encouraged to adopt Cyber Essentials – a minimum baseline in information security. Before we all start bashing it, remember, it is just that –
Categories:
Tags:
Making a Raspberry Pi Photo Frame
This is the updated version of this post. This was my first Raspberry Pi project … and it didn’t get off to a good start. I have since got a new router and lost all means of getting back on to the Pi so I spent some time doing a full rebuild and fixing some
Tags:
Want your content writing?
We are available to create content or ideate.