On the 15th July, around 22:00 BST, premium accounts on Twitter started to pump out messages stating if you send Bitcoins to a given wallet, you will receive double back. I picked this up and tweeted about it at the time, but thought I would consolidate the story into this blog for ease.
10:21 pm LINK
At this point, all we knew was that various accounts were sending a single tweet asking for Bitcoins and they would send it back “doubled.”
For those who have seen scams, this is not new, and the use of Bitcoin just helps to obscure the money flow. The twist in this story was that the accounts under attacked were Verified – these are accounts that have had to go through extra hoops with Twitter to establish their identity. There was plenty of speculation from the security community about how this may have happened from insider threat, SMS re-direction and an old Twitter bug that had been previously identified as not being fixed.
One thing that I picked up on was the bitcoin wallet was the same in all the tweets:
bc1qxy2kgdygjrsqtzq2n0yrf2493p83kkfjhx0wlh
https://www.blockchain.com/btc/address/bc1qxy2kgdygjrsqtzq2n0yrf2493p83kkfjhx0wlh
At its peak, this account had approx £96000 flowing through it.
https://btc.com/bc1qxy2kgdygjrsqtzq2n0yrf2493p83kkfjhx0wlh
https://bitref.com/bc1qxy2kgdygjrsqtzq2n0yrf2493p83kkfjhx0wlh
Which Twitter accounts were affected?
I then started looking at those attacked:
- Apple
- Elon Musk
- Coindesk
- Barack Obama
- Uber
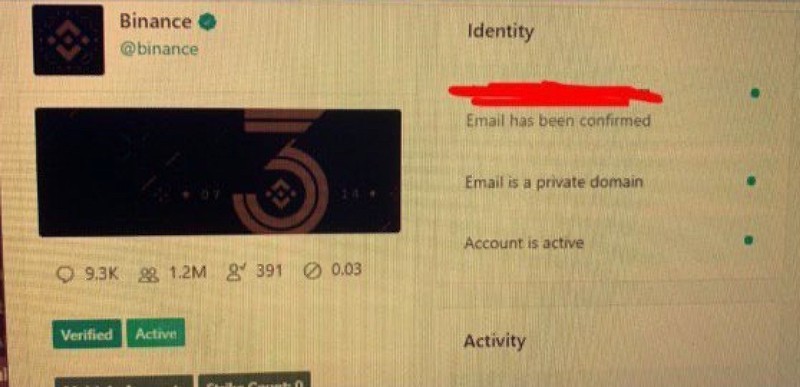
- Binance
- Jeff Bezos
- Coinbase
- Bill Gates
- Joe Biden
These are all smart people with serious media agencies looking after their profiles, so what went wrong?
The Second attack?
In the midst of this and seemingly forgotten was a second set of tweets which were directing people to CryptoForHealth.com. According to this article, the domain had been registered on the same day (15th July 2020).
The domain registration information for the website was found to be publicly available, with CryptoForHealth.com purportedly having been registered by ‘Anthony Elias’ of California using the email address mkeyworth5@gmail.com
This attack didn’t focus on Verified accounts though and felt like a very different kind of attack.
Immediate thoughts?
My initial speculation was not how the attack had happened but instead about:
- Was there two sets of threat actors at play, one with the bitcoin address and one redirecting to CryptoForHealth?
- The timing of this attack
- Which Twitter accounts were not attacked?
Threat Actors
A threat Actor is your adversary, the criminal who is attacking you. In this case, we have two different types of attacks:
- Twitter Verified accounts and Bitcoin Address
- Mainly non-verified accounts and link to website
These two different attack types would indicate different attackers as the style was different. However, these attacks were running concurrently and both related to cryptocurrencies.
Timing
Sometimes merely by looking at when an attack happened, you can see so much more about an incident. For example, this was 10 pm BST.
Around the world, this gives:
2 pm California
5 pm Washington DC
5 am Shanghai
Midnight Moscow
So these attacks are aimed at an American/Canadian market – everyone else is asleep still!
Which Twitter accounts were not affected?
There are thousands of Twitter Verified accounts, but this attack was specific towards mainly US companies and influential people. However, there are some notable misses:
- Google?
- Amazon?
- Retailers?
- Donald Trump?
- Automotive industry?
- Travel industry?
- Charities?
From a psychology perspective, the attacker should have gone for accounts where the followers are most likely to click through and send the money. Instead, the attacker aimed their sites at larger accounts which raised the profile of the attack and netted less money than they could have.
Let it Play
Twitter woke up to the attack and made a smart move and blocked any tweets that referenced the bitcoin wallet. Maybe the attacker was not ready for this action, because we see no new wallets appear after this. We did see plenty of spoof and troll messages, however. My favourite came from the Beer Farmers account:
As a massive gesture of goodwill, we're collecting BTC. You send us yours and we'll spend them partying.
w3t4k3y0ur53cur1tys3r10u5ly0rd0w3#HereForYou #Twittergeddon
— The Beer Farmers (@TheBeerFarmers) July 15, 2020
Brilliant!
The next thing that the Twitter team did was to stop Verified accounts from being able to tweet. This action was a fascinating move in that I think Twitter believed that this was some issue with the verification process. Bear in mind the second attack from above, and it was clear that this was not the case. Even now, there are still non-verified accounts that have those tweets on their profiles (and they are not significant accounts) e.g.
https://twitter.com/toasterrovenn/status/1283515981596327938
https://twitter.com/TheDeadlyFreeze/status/1283519348401999872
Twitter’s response
We are aware of a security incident impacting accounts on Twitter. We are investigating and taking steps to fix it. We will update everyone shortly.
— Support (@Support) July 15, 2020
They responded quickly and kept the community notified. Once Twitter’s support team had identified the issue, Twitter stated that:
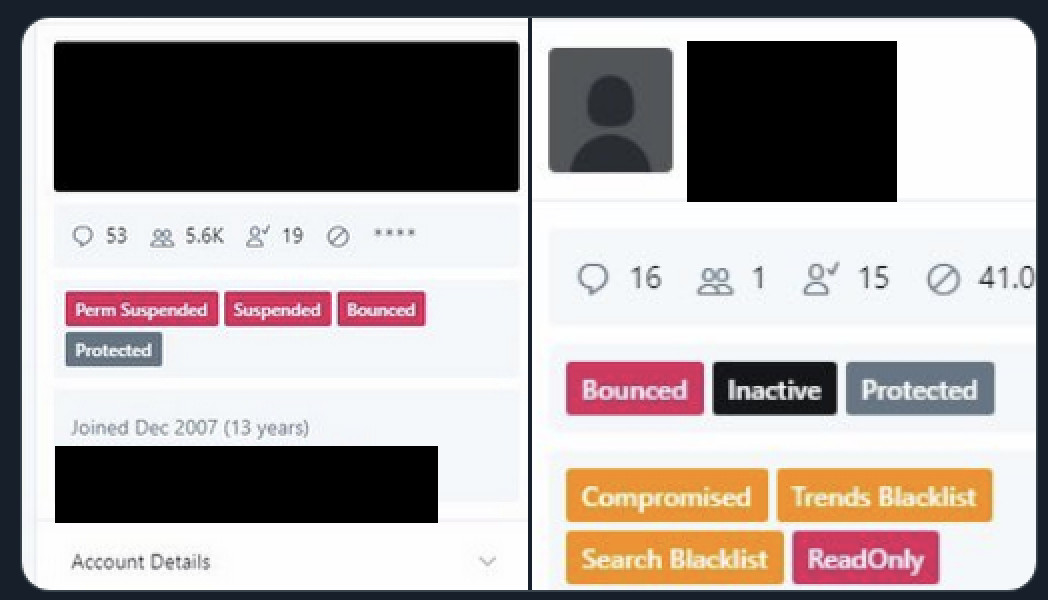
We detected what we believe to be a coordinated social engineering attack by people who successfully targeted some of our employees with access to internal systems and tools.
We know they used this access to take control of many highly-visible (including verified) accounts and Tweet on their behalf. We’re looking into what other malicious activity they may have conducted or information they may have accessed and will share more here as we have it.
Once we became aware of the incident, we immediately locked down the affected accounts and removed Tweets posted by the attackers.
We also limited functionality for a much larger group of accounts, like all verified accounts (even those with no evidence of being compromised), while we continue to fully investigate this.
The most recent update is around the access that the attacker had:
We have no evidence that attackers accessed passwords. Currently, we don’t believe resetting your password is necessary.
Out of an abundance of caution, and as part of our incident response yesterday to protect people’s security, we took the step to lock any accounts that had attempted to change the account’s password during the past 30 days.
As part of the additional security measures we’ve taken, you may not have been able to reset your password. Other than the accounts that are still locked, people should be able to reset their password now.
So how did the hack happen?
The following is a consolidation of several news reports that claim to have spoken to Twitter employees and those close to the incident.
- A member of the Twitter team is approached by an unknown party.
- Member of staff coerced/socially engineered to help the attackers.
- Email address of the account was changed with an internal Twitter tool.
- The insider then has access to the account.
- Attacker sends tweets out.
- Twitter security takes over and starts to lock down Twitter.
- The internal user is probably identified, and the situation ends.
Is that it done now?
Well, I don’t think so. We have seen other Twitter employees abusing their access from deactivating Donald Trumps account to spying for the Saudi regime. Plus, I have a few questions!
The Questions
Here are some questions that I feel are still unanswered:
- If you had access to the back-end system of Twitter, why would you only send crappy tweets?
- You literally had access to the crown jewels, you could have got anything but instead you send spam? Is this actually a distraction or calling card to say “I woz here” and is there instead a bigger attack hiding there?
- Why did the attacker not steal Direct Messages? Imagine the value of politician and celebrity Direct Messages!
- DMs are where we take our conversations “offline.” Imagine the damage you could impact by grabbing the DMs of anyone? If you had access to Apple, why not grad the AppleSupport DMs and get all the personal data that people share with the support people?
- If this was an internal person who became compromised, what leverage did the attacker have on the staff member?
- Let us assume that an internal person was the issue, it was so risky for that member of staff to do this that it does not feel like a simple attack, this feels like they had something on the engineer which caused them to take such a risk.
- Was this one attack or two?
- We know there were two styles of attack, so are there two adversaries that run concurrently? Perhaps bought the same 0-day from the same dark web site and once it was used, the owner ditched it?
- Who was the attacker – a group or an individual?
- Was this is a single person? Was this an APT? Was it an organised criminal gang?
- Why stop with just the accounts they had?
- Why only hit the small amount of accounts? They couldn’t have hoped to fly below the radar with the accounts that they did choose so why not go all-out on it?
- Was there some political message behind this?
- Looking at the mapping of names, Joe Biden and Barack Obama – both Democrats. Apple has had its run-ins with the current US administration and not a single Republican hit? There looks to be a mighty big coincidence there for sure.
- What else was taken?
- Twitter have answered all the questions about the attack as we saw it. They have been careful in their wording that passwords were not stolen, but how long before we see what else was done?
- Was this about the money, or was this to prove a point?
- This is a poor scam on the best of days and was picked up very quickly. So either the attacker was happy with any small amount of money that they received, or, they were doing this to prove a point that they could do this attack.
- What security controls are missing that enables Twitter back-end staff to have this access?
- This will be an infosec salesman’s dream – if they’d bought our solution, their staff couldn’t have done this attack, and I get that. It does feel like if you have access to this magic tool you literally have IDDQD god-mode into every Twitter account. That seems a little off to say the least?
Tips for you
- Add 2-factor authentication to your account on social media. That way it is harder for an attacker to be able to log in to the account.
- If you are still worried about your account, change your password (remember, lengthy and complicated and for preference, use a password manager).
- Ask your marketing team have they secured their accounts.
- Speak to your security teams about how this could be caught in your organisation.
- Create a plan should you be attacked like this.
- Use this incident to educate your teams about social engineering attacks.
- Look through apps attached to your account and remove ones you don’t need anymore.







Leave a Reply